Cyberattacks aren't just for multinationals – here's what small firms need to know
SMEs are less exposed to sophisticated attacks, but they still need to take precautions.
SMALLER BUSINESS OWNERS may think the approach to dealing with cyber threats is radically different to multinationals – but the main issues are largely the same.
It’s critical for any organisation to identify the most damaging and likely threats that could really impact their business.
Large organisations may be the target of highly sophisticated attacks and therefore need to go into greater depth when profiling potential attackers.
SMEs tend to be less exposed to such attackers and therefore may not need to go to great extents to understand their modus operandi – but they still have to take precautions.
Here’s what small businesses need to know about cybersecurity:
Detection
It may be a stretch for most SMEs to monitor for cyberattacks on a 24/7 basis.
However, training employees to be aware of how to spot – and report – attempted attacks is one area where smaller firms can have the most impact. Employees and third parties are part of your first line of defence; your ‘human perimeter’.
Raising employee awareness is the first step, followed by establishing clear reporting lines – for example, encouraging employees to report if they have accidentally clicked on a phishing link.
Making it acceptable for someone to put their hand up and admit a mistake without fear of censure is important as it can help contain an attack at a very early stage. This is as much a cultural issue as one of policy.
On the IT side, it is also useful to have someone looking at alerts and log files for clues such as multiple failed login attempts, odd network traffic or unauthorised software being installed.
Response
The organisation’s response to an attack is absolutely critical, and it should be set out as a response plan that is frequently reviewed and updated. It should cover areas such as:
- Reporting an incident
- The immediate steps to limit the damage
- Containing the incident
- Investigating the root cause
- Eradicating the root cause and follow up
Most organisations will have a crisis management plan in place. The cyber incident response plan should form an important part of it.
Testing the plan with simulated exercises
A response plan that has not been tested is as useless as having no plan at all. Putting the plans into practice is not only a good idea, but for some sectors it’s a regulatory requirement.
Simulation exercises can be instructive and even fun – in fact it’s good to add some humour to the scenarios sometimes as it helps with engagement and learning.
There are three levels of exercise and teams involved in them.
Bronze team: This typically lasts six to eight weeks and involves the security team fighting back against ethical hackers and trying to shut them down. This tests the organisation’s technical abilities to detect and respond to sophisticated attackers.
Silver team: This is one of the most important exercises and involves incident managers coordinating and implementing the response plan. The silver team will keep notes of everything that happens, manage calls and notifications, media relations and communications, and consult lawyers. They follow the plan and make sure everyone is on track.
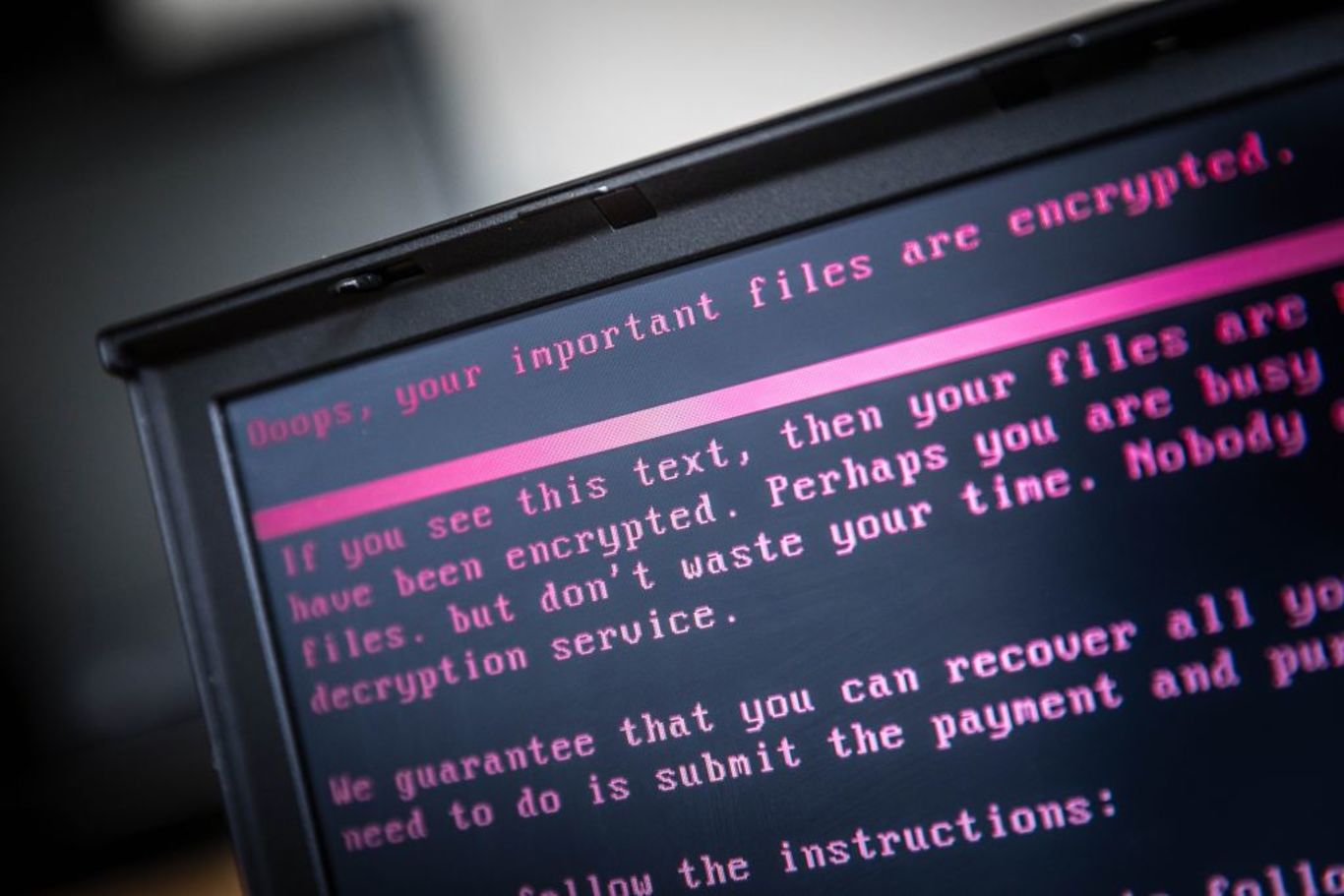
Gold team: This involves the C-suite making decisions in critical situations without all the facts available. For example, an exercise might start off with a simple breach, handled by the bronze and silver teams, which then turns into a ransom demand. This requires the gold team to assess whether the demand is real, decide whether they should pay it, whether to involve the police and what to say to the media.
Rather than a fire drill-style exercise, cyberattack simulations work best in phases that ramp up the complexity of the challenge.
This echoes the reality of serious cyberattacks. For example, a pharma company might have to decide the order in which manufacturing plants come back online – the one manufacturing life-saving cardiac drugs or the one that makes paracetamol?
Good exercises push and challenge everyone. In a recent exercise we conducted, a large financial services company had lost customer data and a lawyer was trying to bring a class action lawsuit from customers demanding compensation.
The insurance company’s lawyer responded quite aggressively and suggested counter-suing for costs. But in the next phase of the exercise, we imagined one of the customers appearing on live talk radio, responding furiously to the insurance company’s counter-threat and impacting the company’s brand – which gave the in-house lawyer cause to rethink their approach.
Exercises such as this bring to light some key challenges:
1. Who is in charge? If no one is making and transcribing decisions, this needs to happen.
2. What will you say to the media? Having prepared and legal-approved statements ready to go in the event of a data breach could limit damage significantly.
3. Who is your cyber ecosystem? Identifying who can help you, and which regulators to contact, is also great planning. The midst of a crisis is not the time to start trying to find contacts and impacted parties.
Having these answers, resources and exercises in place can help SMEs protect themselves against damaging cyberattacks.
Simon Collins is director of EY‘s cybersecurity advisory unit. Additional contributions by EY partner Ivan O’Brien